

Proactive Vulnerability Assessment
Identify and remediate security gaps across your entire digital attack surface before adversaries exploit them.






Comprehensive Security Solutions
Specialized dimensions of cybersecurity tailored to protect your assets, compliance, and future.

Security Assessment
Identify and remediate security gaps across your entire digital attack surface before adversaries exploit them.

Compliance Audit
Ensure your organization meets global security standards and avoids costly regulatory penalties.

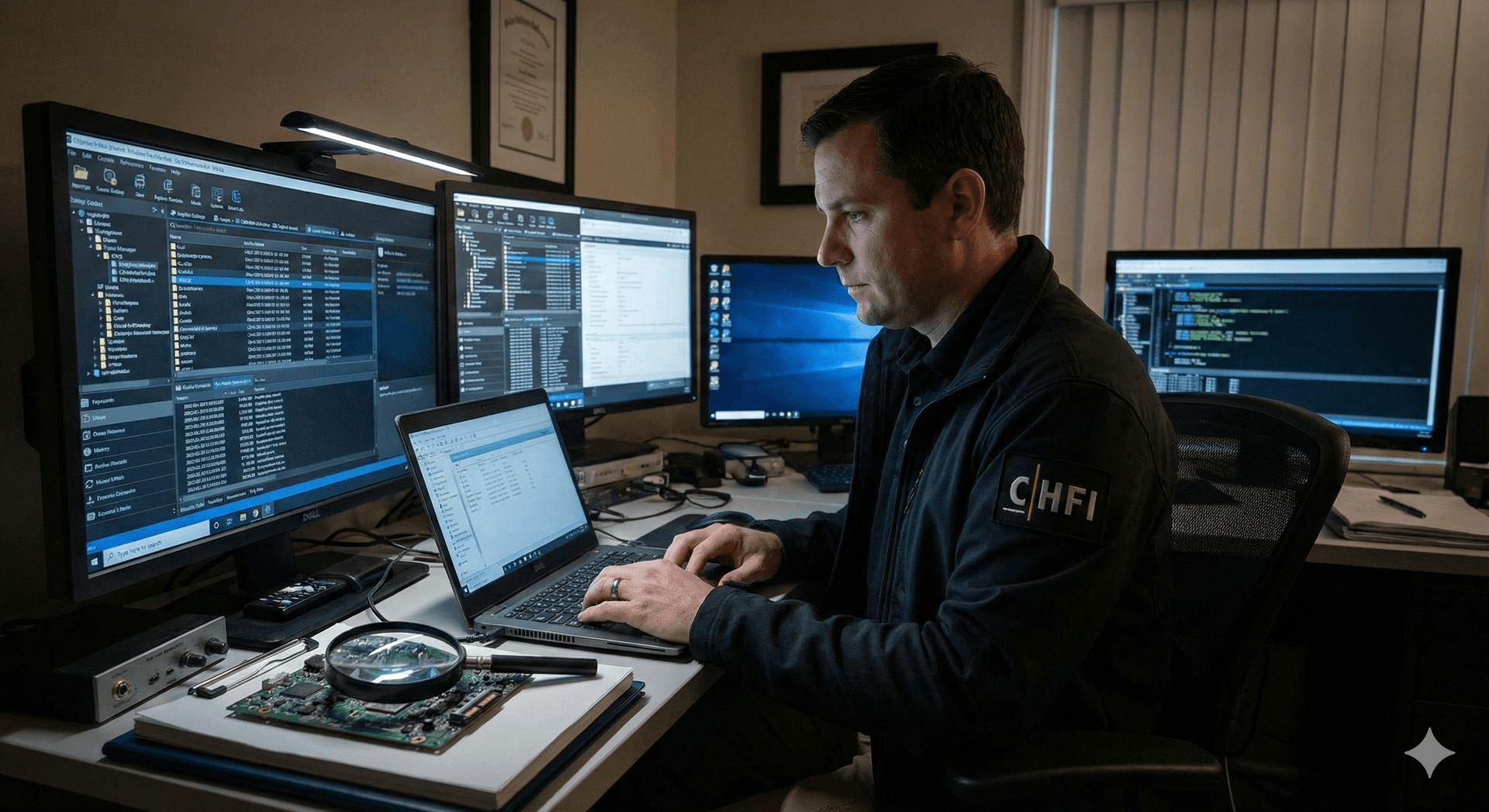
Forensics & Malware
Rapid response capabilities to contain threats, analyze breaches, and recover operations.
12+
Years of Experience
500+
Enterprise Clients
50+
Security Experts
Trusted Across Industries
From fintech to healthcare, we secure organizations across all sectors

Banking & Finance
In an ecosystem where trust is currency, we provide an impenetrable shield for your digital assets. Our approach goes beyond simple compliance, deploying predictive threat modeling and real-time transaction analysis to neutralize financial fraud and SWIFT vulnerabilities before they can destabilize operations.
/// Key Solutions
- Real-time Transaction Monitoring
- Advanced Fraud Detection Systems
- PCI-DSS & ISO 27001 Compliance
- Zero Trust Architecture Implementation
Security in Action
See how eHack Global Technology protects organizations from critical threats
(Names changed for confidentiality)
Securing 10L+ Student Records from a Critical SQL Injection
The Breach: A critical vulnerability in the university's examination portal exposed sensitive personal data and grade sheets of over 10 lakh students to potential dark web leaks.
The eHack Global Technology Solution:
- ✓Identified blind SQL injection points within 2 hours
- ✓Deployed emergency WAF patches immediately
- ✓Sanitized database queries & implemented RBAC
"eHack's rapid response saved our reputation. Their team identified holes our previous auditors missed in months."
— Dr. Rajesh Verma, Dean of Technology
Around-the-World Protection
Built on 18+ Advanced Cyber Defense Centres ensuring seamless 24/7 security.

18+
Advanced Cyber Defense Centres
24/7
Continuous Threat Monitoring
200+
Countries & Regions Covered
Empowering Cyber Defenders with Intelligence and Action
Where Learning Meets
Real-World Defense
At eHack Global Technology, we don't just teach cybersecurity; we train the next generation of digital architects to defend, respond to, and lead in an increasingly hostile digital landscape.
Our curriculum goes beyond theoretical frameworks to deliver battle-tested, actionable skills that are immediately applicable in high-stakes environments. We believe that in a world of evolving threats, education must keep pace with the speed of innovation.
Explore ProgramsLive Cyber Range Simulations
Hands-on labs that mirror today's advanced threat landscapes, allowing you to practice defense in real-time.
Expert-Led Mentorship
Sessions guided by industry veterans with 15+ years of frontline experience in securing global enterprises.
Industry-Aligned Curriculum
Coursework developed in collaboration with leading C-CISOs to ensure relevance in the modern job market.
Your Trusted Security Partner
We combine cutting-edge tools with expert human analysis to deliver unmatched security insights
Global Expertise
Our team has experience securing enterprises across 20+ countries with diverse industry knowledge.
Fast Turnaround
Get detailed reports within 48-72 hours with prioritized vulnerability findings.
Certified Professionals
CEH, OSCP, CISSP certified experts with 10+ years of experience.
Zero False Positives
Every finding is manually verified to ensure actionable insights.
Compliance Ready
Reports aligned with ISO 27001, PCI DSS, GDPR, and industry standards.
Dedicated Support
24/7 support with free re-testing after remediation.
Ready to Secure Your Enterprise?
Get a comprehensive security assessment from our certified experts. Identify vulnerabilities before hackers do.
Social Impact & Strategic Growth
Driving positive change through cyber literacy while expanding our global footprint through strategic partnerships.
Empowering Society Through Cybersecurity, Employability & Emerging Technologies
Join our mission to bridge the skill gap and build a safer digital future for everyone.
Build Your Educational Empire with eHack Global Technology Franchise
Build a thriving educational venture with India's premier cybersecurity global technology firm.